As part of a 4th year module, some students and I performed some test on Pi-hole, a network level ad blocker for your LAN. We wrote a short article about the experience and published it on Medium.
You’ll find the original piece here, but I’ll copy it after the jump to keep things handy for myself on the blog! Written by Andrew Brennan, Gianluca Zuccarelli and myself (they did most of the work BTW!)
Falling Down a Pi-hole
Andrew BrennanApr 23·4 min read
What is Pi-hole
Pi-hole is a software tool which claims to:
- Provide network-wide protection
- Block in-app advertising
- Improve network performance
- Monitor statistics
Pi-hole can be installed on a number of devices, such as Raspberry Pi’s (hence the name!), Docker containers or remote AWS EC2 instances. Pi-hole offers network wide protection by blocking ads at the network level rather than a browser plugin. The main benefit to this is that it blocks in-app advertisements on mobile phones and smart connected devices. This protects user devices connected to your network from online trackers and advertisements without requiring them to install any software themselves.
As a college project, we decided to test the ad-blocking capabilities.
What we did
We tried two different setups with the Pi-hole, which essentially set up a custom DNS sinkhole. The first method was to install the Pi-hole software on an AWS EC2 instance. Configuration instructions can be found here. There were two main drawbacks, the first was that you only have 750 hours a month of EC2 usage on the free-tier (and we’re poor students!). The second drawback, which was more problematic, was that the Pi-hole DNS sinkhole was completely open to the world. You could limit the traffic to the EC2 instance if you had a static IP address, however we did not have this luxury. The second method we used was to set up a Pi-hole as a dedicated Raspberry Pi device on the local network. The main benefits are that it can only be accessed locally and the local router can be configured to forward all DNS requests to the static IP address of the Raspberry Pi. This meant all traffic on the local network was being serviced by the Pi-hole device. The setup on the Raspberry Pi took less than 5 minutes.
Once set up, we tested Pi-hole’s effects on PCs and mobile devices in two locations (with a seperate Pi-hole device at each location). For desktops and laptops, we disabled all ad-blockers to see if we noticed any changes. Beforehand we were running uBlock Origin and Privacy Badger on Chrome, or the built in privacy features of Brave. For mobile, we switched between WiFi and 4G connections (to bypass Pi-hole) and then then browsed the internet and tested some mobile games to see if we could notice the difference. We also examined the Pi-hole activity logs to see if they matched our observations. The tests in Location A ran for 7 days and the tests in Location B ran for 23 days.
Results
We compared and contrasted the results of the two Pi-hole instances. It seemed that both setups had pretty similar outcomes. Around 18% of ad requests were blocked at Location A and approximately 12% of total requests blocked at Location B. Pi-hole provides a lot more information in the logs, but those are the headline figures. The biggest offenders appeared to be Google ad servers, Amazon device metrics and WhatsApp data collection.
Observations
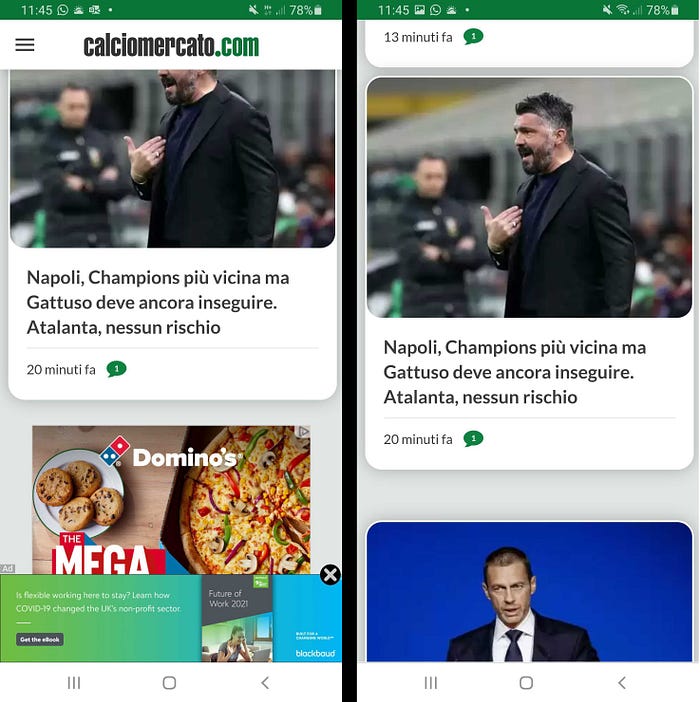
When asking other members of the household if they had noticed any changes, the answer was a resounding no. YouTube ads for example, were very rarely blocked. If someone was already accustomed to using ad blockers on their browser, Pi-hole is probably not as effective a solution. Where the Pi-hole performed better was on mobile devices (it is not common to have ad-blockers built into apps). The Pi-hole didn’t block everything, but the volume of ads on games and news websites was definitely lower. This difference was most apparent when switching between WiFi and 4G on the phone (therefore enabling/disabling the Pi-hole).
Additionally, network performance at Location B was significantly reduced. However, we’re not sure if this is due to a router or ISP issue and is most likely a coincidence. The network issues have persisted even after the Pi-hole was disabled, so it’s probably a larger problem.
Conclusions
If you have an old Raspberry Pi kicking about, this is a fun little project. It’s pretty easy to get started and set up. There is a noticeable reduction of adverts on mobile devices, but you will probably still want to use ad-blockers on your PC/laptop browser. It is possible to configure Pi-hole with a more aggressive ad blocking approach, which we didn’t do. The more blocklists you add, the more likely you are to encounter false positives. This is something we will definitely try in the future. Pi-hole can be configured to dynamically update its blocklists. It might be an effective way to enforce content controls on a local network. For example, ensuring minors aren’t served explicit content.
Overall, Pi-hole is a good tool that’s definitely worth considering if you’re looking for a free and relatively simple way to filter content on your local network.
This article was written by Andrew Brennan, Gianluca Zuccarelli and Robert O’Connor from Waterford Institute of Technology, Ireland.

